Cybersecurity Risks in Legacy Rail Fleets: Why Older Trains Still Matter
As rail operators invest in new fleets with advanced digital systems, it’s easy for attention to shift away from legacy rolling stock. But from a cybersecurity perspective, that can be a costly oversight.
For decades, trains relied on analogue controls or isolated onboard systems with no outside connections. This made them effectively “secure by design.” As a result, older trains are often assumed to be less exposed to cyber risks. In reality, their growing integration with modern systems, and reliance on outdated protections, can introduce new vulnerabilities.
Why could older fleets be a cybersecurity weak spot?
Upgrades introduce new digital connections, which can expose legacy fleets to risks they were never designed to withstand.
As legacy trains are upgraded to meet today’s operational needs – improving passenger experience, boosting efficiency or enabling smarter maintenance – more digital technologies are being added. These upgrades bring clear operational benefits, but they also reshape the cybersecurity landscape.
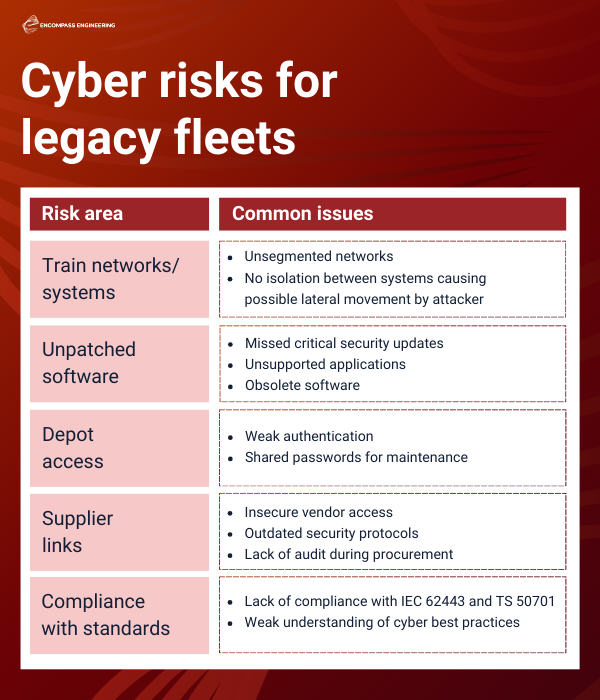
Segmented networks: Many older fleets still operate on unsegmented networks, where there is no clear separation between different functional systems. Without defined security boundaries, an attacker who gains access to one part of the network can often move laterally across others with little resistance.
Outdated technology: This challenge is compounded by outdated software and hardware. Unlike modern systems that benefit from regular security updates, legacy components may go years without patches due to discontinued vendor support, missing documentation, or gaps in maintenance routines. These vulnerabilities can make older fleets an attractive target for cyber attackers.

Are depot practices a cyber risk?
Yes – because depot processes often rely on trust and routine, which can lead to inconsistent security controls and create avoidable cyber risks.
Train depots usually have formal security policies, but in practice these controls often depend on trust and established habits. Technicians are expected to follow best practice, yet cybersecurity can slip down the priority list when operational pressures take over.
Depots can also be overlooked within wider organisational cybersecurity strategies, which leads to inconsistent application of essential controls, such as software access and authentication. A common example is the use of weak or shared passwords on maintenance laptops. Standards such as IEC 62443 and CLC/TS 50701 make clear that strong authentication – including complex and unique credentials – is critical for protecting industrial systems. The same requirements apply to legacy fleets, which rely heavily on depot‑based diagnostics and updates.
Do suppliers pose a cybersecurity risk?
Suppliers can introduce hidden vulnerabilities, so their security practices must meet the same standards as those used by operators.
A significant source of cyber risk for both new and legacy fleets comes from the supply chain. Train operators may have strong controls for managing third‑party access, but gaps can still appear when external suppliers are involved.
Rail systems rely heavily on vendors for hardware updates, software support and diagnostics. However, suppliers may not always apply the same level of cybersecurity rigour as operators. If their practices are weaker – whether in authentication, remote access or software handling – they can inadvertently create entry points for attackers.
To reduce this risk, suppliers need to follow the same strict security expectations as anyone accessing operational rail systems.
What are the top cyber risks facing legacy fleets?
Legacy fleets face significant cyber risks because they were never designed for today’s connected rail environment.
As rail operators invest in modern fleets with advanced digital systems, legacy rolling stock is often overlooked from a cybersecurity perspective.
Yet older trains can pose significant risks. Many were not designed with cybersecurity in mind and may run on unsegmented networks, giving attackers easier access. Ageing software and a lack of updates further expose critical vulnerabilities.
Risks also extend to depots, where inconsistent security practices and weak vendor controls can leave systems open to attack.
Protecting legacy fleets requires a comprehensive strategy that includes system updates, secure maintenance, and supply chain security – all underpinned by evolving standards, such as TS 50701 and the upcoming IEC 63452.
Ready to improve your cyber resilience?
Cybersecurity threats continue to grow across the rail industry, and protecting your systems is essential for safe and reliable operations.
At Encompass, we help operators and train owners understand their vulnerabilities, assess real‑world risks and make informed decisions with confidence. Our approach to cyber assurance gives you a clear picture of your exposure and practical steps to strengthen resilience across both modern and legacy fleets. Learn more about our approach to cyber assurance for rail.
See how we helped a train owner to Strengthen their cybersecurity for a new train fleet.